Techworx LLC Blog
How it works: Microsoft Multi-Factor Authentication
Working remotely can be risky for your organization when it comes to cybersecurity. It would be a sure bet that your employee's home networks are not as secure as the office network they are used to working in. To add fuel to the fire, many of your employees are sharing their home network with spouse's and children's devices that may have little to no security features and most likely little control of where they are browsing.
So how can you protect your employees and your organization's data? Through implementing multi-factor authentication you can ensure that access to your data is secure. Multi-factor authentication is a process where a user is prompted during the sign-in process for an additional form of identification, such as to enter a code on their cellphone or to provide a fingerprint scan. If this sounds familiar, it's because most financial institutions already require you to use multi-factor authentication to access your accounts.
If you only use a password to authenticate a user, it leaves an insecure vector for attack. If the password is weak or has been exposed elsewhere, is it really the user signing in with the username and password, or is it an attacker? When you require a second form of authentication, security is increased as this additional factor isn't something that's easy for an attacker to obtain or duplicate.
Microsoft Multi-Factor Authentication works by requiring two or more of the following authentication methods:
- Something you know, typically a password.
- Something you have, such as a trusted device that is not easily duplicated, like a phone or hardware key.
- Something you are - biometrics like a fingerprint or face scan.
TechWorx can register your organization for Multi-Factor Authentication through your Microsoft 365 license. We can define what forms of secondary authentication can be used and even implement single sign on for your employees. Microsoft Multi-Factor Authentication can also be required when users perform a self-service password reset to further secure that process.
Microsoft Multi-Factor Authentication helps safeguard access to data and applications while maintaining simplicity for users. It provides additional security by requiring a second form of authentication and delivers strong authentication via a range of easy to use authentication methods.
Your applications or services don't need to make any changes to use Microsoft Multi-Factor Authentication. The verification prompts are part of the Microsoft Azure AD sign-in event, which automatically requests and processes the MFA challenge when required.
Available verification methods
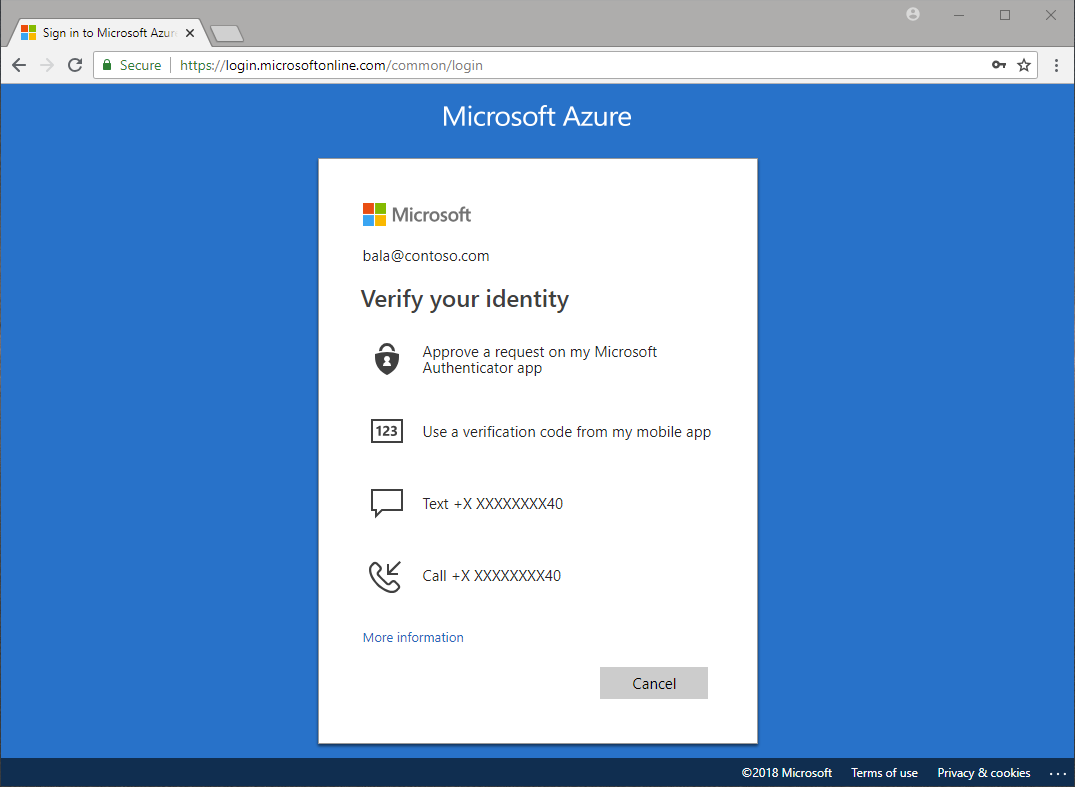
When a user signs into an application or service and receive an MFA prompt, they can choose from one of their registered forms of additional verification.
The following additional forms of verification can be used with Microsoft Multi-Factor Authentication:
- Microsoft Authenticator app on cellphone (easiest and most common)
- OATH Hardware token
- SMS (Text Message)
- Voice call
How Microsoft Multi-Factor Authentication works
Employees will first sign-in with their username and password. This will prompt the activation of the MFA and launch the Microsoft Authentication app on their cellphone. The Microsoft Authentication app will ask the users to accept or deny the authentication. If they were logging in they would accept and gain access to their organization's data. If they were not logging in and were prompted by the Microsoft Authentication app, they would choose to deny which would block someone who was attempting to gain access to your organization.

Next steps
To discuss enabling Microsoft Multi-Factor Authentication for your organization email or call 814-806-3228 to learn more.
Comments

